Blockchain: The Foundational Ledger of Decentralized Trust
At the heart of virtually every cryptocurrency lies blockchain technology, a distributed, immutable ledger that meticulously records transactions across a network of computers. Unlike traditional centralized databases, where a single entity controls and maintains the ledger, a blockchain is decentralized. This means that instead of one server or organization holding all the data, copies of the ledger are distributed across numerous nodes (computers) in the network. This fundamental shift from centralized control to a peer-to-peer architecture is what imbues blockchain with its characteristic resilience and resistance to censorship.
The term “blockchain” itself is descriptive: it is a chain of “blocks,” where each block contains a batch of transactions. When a new block is created, it is linked cryptographically to the previous block, forming an unbroken chain extending back to the very first block, known as the “genesis block.” Each block includes a cryptographic hash of the previous block, a timestamp, and transaction data. This cryptographic linkage is crucial for security; any alteration to a past block would change its hash, thereby invalidating all subsequent blocks and immediately signaling tampering to the network. This immutability is a cornerstone of blockchain’s integrity, ensuring that once data is recorded, it cannot be retroactively altered or deleted, a characteristic highly valued in auditing and maintaining secure records, perhaps even for intricate maintenance logs far more critical than those pertaining to the 4 most common maintenance issues for houses of worship, which, while important for asset longevity, typically lack the same level of cryptographic immutability in their record-keeping.
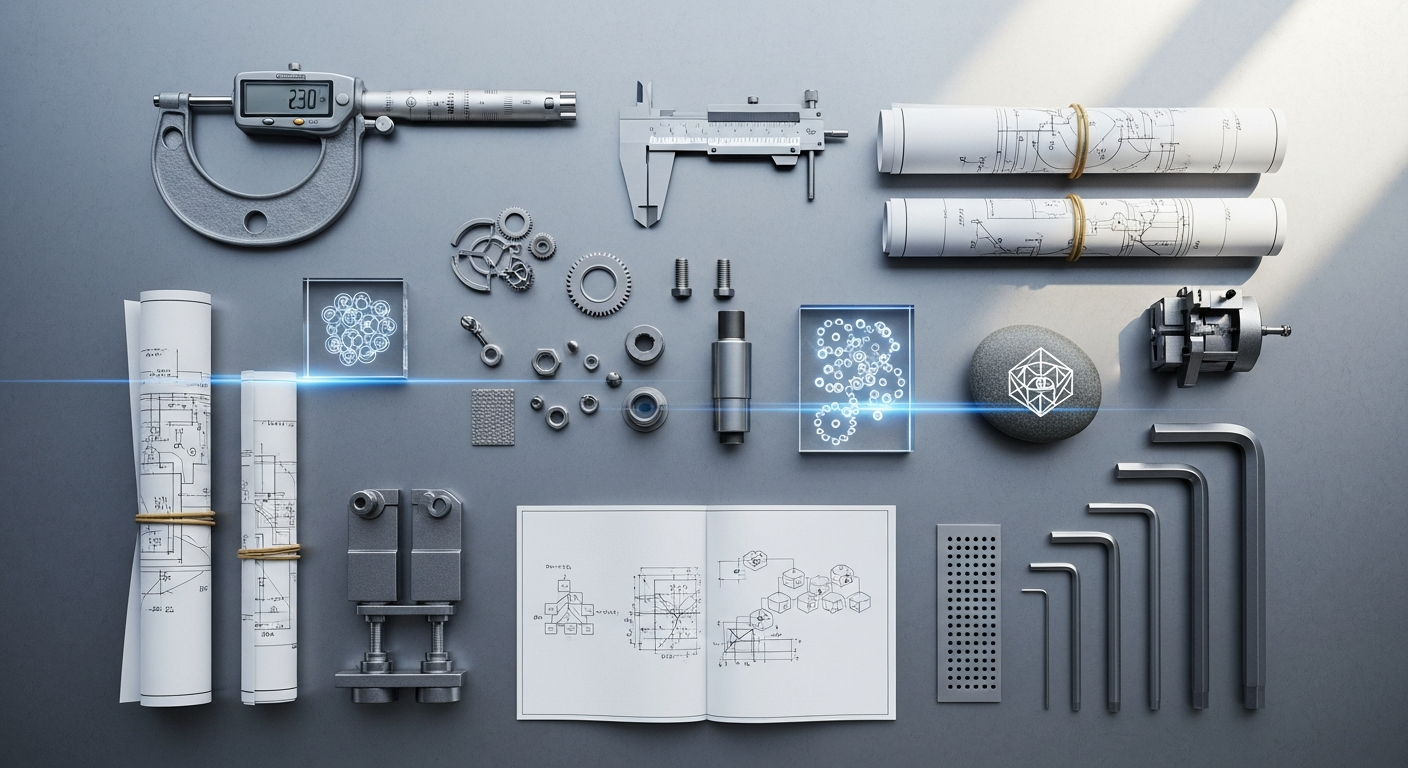
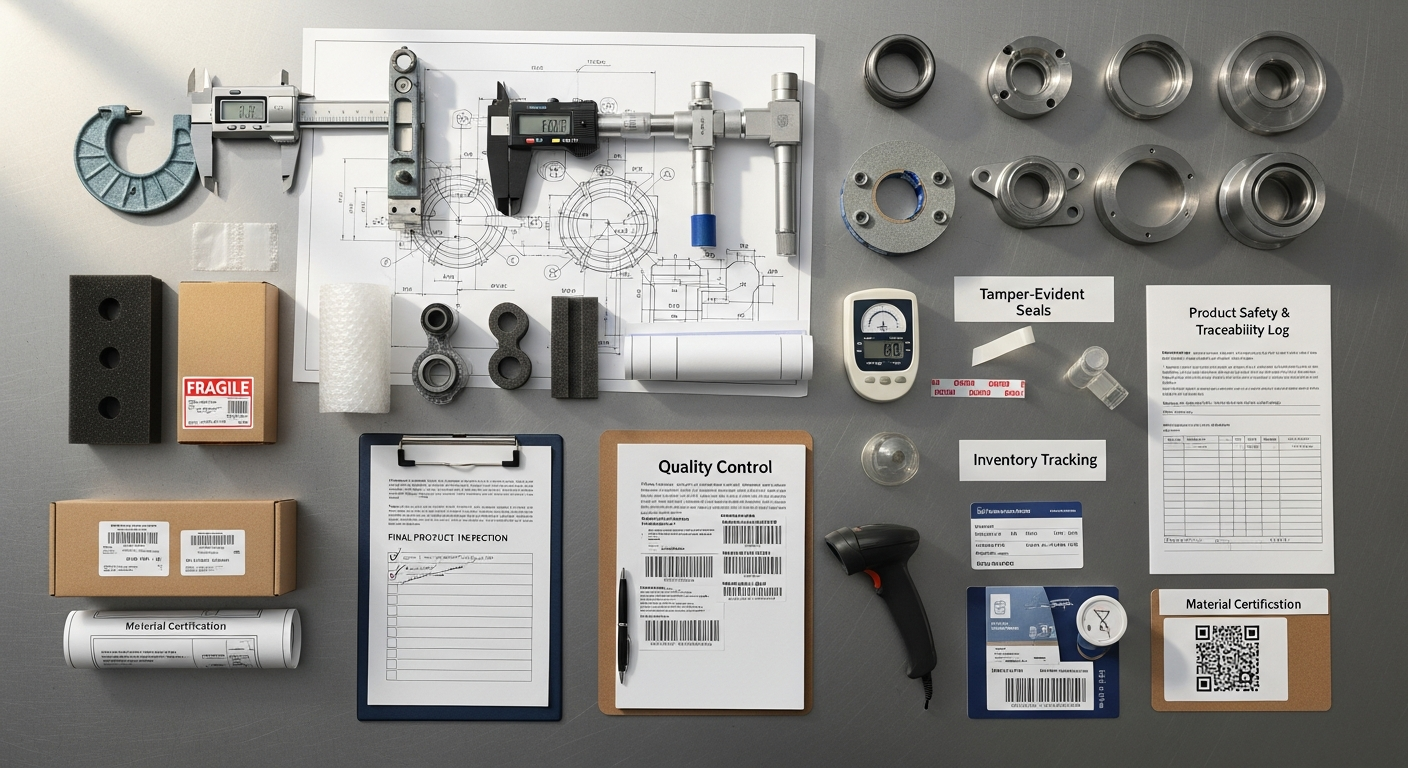
The process of adding new blocks to the chain involves a consensus mechanism, which we will explore in detail later. For now, it’s important to understand that new transactions are broadcast to the network, collected by network nodes into a block, and then validated according to the network’s rules. Once validated and added, the new block is propagated across the entire network, ensuring all participants have an updated, identical copy of the ledger. This distributed consensus eliminates the need for a central authority to verify transactions, replacing it with cryptographic proof and network agreement. For manufacturing, this decentralized and immutable record-keeping capability presents transformative potential, particularly in supply chain management where the verifiable provenance of materials and components can significantly enhance trust and efficiency, directly impacting how a manufacturing brand is perceived and grown through transparency.
Furthermore, the transparency inherent in public blockchains means that all transactions, while often pseudo-anonymous (linked to cryptographic addresses rather than real-world identities), are publicly viewable. This open auditability stands in stark contrast to opaque centralized systems and provides a robust framework for accountability. The combination of decentralization, immutability, and transparency makes blockchain a powerful technology for creating secure, auditable, and resilient systems – attributes increasingly sought after in an interconnected industrial landscape where data integrity is paramount.
Cryptography: The Unseen Shield of Digital Transactions

While blockchain provides the structural framework for a decentralized ledger, it is cryptography that provides the essential security and integrity necessary for cryptocurrency to function without trusted intermediaries. Cryptography, the science of secure communication in the presence of adversaries, underpins every aspect of a cryptocurrency transaction, from securing individual user funds to validating the entire network’s activity.
The primary cryptographic tool employed in cryptocurrency is public-key cryptography, also known as asymmetric encryption. This system relies on a pair of mathematically linked keys: a public key and a private key. The public key can be freely shared and acts like a bank account number, while the private key must be kept secret and functions as the password or signature authority for that account. When a user wants to send cryptocurrency, they use their private key to “sign” the transaction. This digital signature proves ownership of the funds without revealing the private key itself. Crucially, anyone on the network can use the sender’s public key to verify that the signature is valid and that the transaction indeed originated from the rightful owner, preventing repudiation. This mechanism ensures that only the owner of the private key can authorize spending their cryptocurrency, providing a robust layer of security against unauthorized access and double-spending.
Another fundamental cryptographic primitive is the cryptographic hash function. A hash function takes an input (data of any size) and produces a fixed-size output, known as a hash value or digest. Key properties of cryptographic hash functions include:
- Determinism: The same input always produces the same output.
- Pre-image resistance: It’s computationally infeasible to reverse the hash function to find the original input from its hash.
- Second pre-image resistance: It’s computationally infeasible to find a different input that produces the same hash as a given input.
- Collision resistance: It’s computationally infeasible to find two different inputs that produce the same hash output.
In blockchain, hash functions are used extensively. Each block’s header contains a hash of the previous block, creating the cryptographic link that forms the chain. Hashes are also used to represent transactions efficiently within a block through a Merkle tree structure, allowing for quick and secure verification of transactions within a block without needing to process the entire block’s data. Furthermore, the mining process in many cryptocurrencies relies on finding a specific hash output, demonstrating a “proof of work” that secures the network.
Digital signatures, built upon public-key cryptography and hash functions, are critical for transaction integrity. When a transaction is initiated, the sender’s software first hashes the transaction details. This hash is then encrypted using
Recommended Resources
You might also enjoy Child Support Rights And Resources from Protect Families Protect Choices.
Explore Passive Income Ideas 2026 for additional insights.